Reflected XSS
There is no sanitization on the users input. This allows a attacker to distrubte a JavaScript payload using the service.
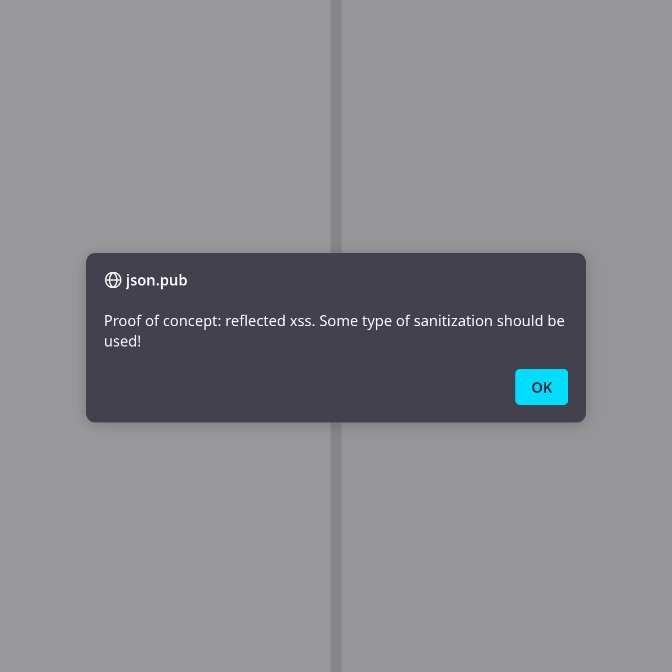
For eg. this payload will show the user a alert.
<img src=x onerror="alert('test')" />
proof-of-concept:
https://json.pub/?d=DwSwtg5gBAzgTgYwLwA8oHsB2BTOd1xIBEAhgDa4AuAFAOQAK%2B6AZhqwlgtgA6UBcUONmYUElbABMoKGDAB0UAMrow2KJQCe3NS1glMISiABeJI1lgALdAFcyUgEZqbMSQEJaASiJQA9AD4AKCA
Please authenticate to join the conversation.
Upvoters
Status
Completed
Board
📑 json.pub
Date
Over 1 year ago
Subscribe to post
Get notified by email when there are changes.
Upvoters
Status
Completed
Board
📑 json.pub
Date
Over 1 year ago
Subscribe to post
Get notified by email when there are changes.